Description
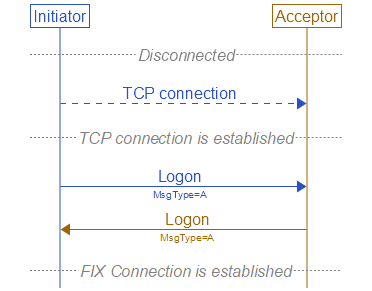
The Logon <A> message authenticates a user establishing a connection to a remote system. The Logon <A> message must be the first message sent by the application requesting to initiate a FIX session.
The HeartBtInt <108> field is used to declare the timeout interval for generating heartbeats (same value used by both sides). The HeartBtInt <108> value should be agreed upon by the two firms and specified by the Logon initiator and echoed back by the Logon acceptor.
Upon receipt of a Logon <A> message, the session acceptor will authenticate the party requesting connection and issue a Logon <A> message as acknowledgment that the connection request has been accepted. The acknowledgment Logon <A> can also be used by the initiator to validate that the connection was established with the correct party.
 Successful Logon
Successful Logon
The session acceptor must be prepared to immediately begin processing messages after receipt of the Logon <A>. The session initiator can choose to begin transmission of FIX messages before receipt of the confirmation Logon <A>, however it is recommended that normal message delivery wait until after the return Logon <A> is received to accommodate encryption key negotiation.
The confirmation Logon <A> can be used for encryption key negotiation. If a session key is deemed to be weak, a stronger session key can be suggested by returning a Logon <A> message with a new key. This is only valid for encryption protocols that allow for key negotiation. (See the FIX Web Site's Application notes for more information on a method for encryption and key passing.)
The Logon <A> message can be used to specify the MaxMessageSize <383> supported (e.g. can be used to control fragmentation rules for very large messages which support fragmentation). It can also be used to specify the MsgTypes supported for both sending and receiving.
Structure
| Tag | Field Name | Req'd | Comments | |
|---|---|---|---|---|
| Component Block - <StandardHeader> | Y | MsgType <35> = A | ||
| 98 | EncryptMethod | Y | (Always unencrypted) | |
| 108 | HeartBtInt | Y | Note same value used by both sides | |
| 95 | RawDataLength | N | Required for some authentication methods | |
| 96 | RawData | N | Required for some authentication methods | |
| 141 | ResetSeqNumFlag | N | Indicates both sides of a FIX session should reset sequence numbers | |
| 789 | NextExpectedMsgSeqNum | N | Optional, alternative via counterparty bi-lateral agreement message gap detection and recovery approach (see Volume 2 - "Logon Message NextExpectedMsgSeqNum Processing" section) | |
| 383 | MaxMessageSize | N | Can be used to specify the maximum number of bytes supported for messages received | |
| Component Block - <MsgTypeGrp> | N | |||
| 464 | TestMessageIndicator | N | Can be used to specify that this FIX session will be sending and receiving "test" vs. "production" messages. | |
| 553 | Username | N | ||
| 554 | Password | N | Note: minimal security exists without transport-level encryption. | |
| 925 | NewPassword | N | Specifies a new password for the FIX Logon. The new password is used for subsequent logons. | |
| 1400 | EncryptedPasswordMethod | N | ||
| 1401 | EncryptedPasswordLen | N | ||
| 1402 | EncryptedPassword | N | ||
| 1403 | EncryptedNewPasswordLen | N | ||
| 1404 | EncryptedNewPassword | N | Encrypted new password- encrypted via the method specified in the field EncryptedPasswordMethod <1400> | |
| 1409 | SessionStatus | N | Session status at time of logon. Field is intended to be used when the logon is sent as an acknowledgement from acceptor of the FIX session. | |
| 1137 | DefaultApplVerID | Y | The default version of FIX messages used in this session. | |
| 1407 | DefaultApplExtID | N | The default extension pack for FIX messages used in this session | |
| 1408 | DefaultCstmApplVerID | N | The default custom application version (dictionary) for FIX messages used in this session | |
| 58 | Text | N | Available to provide a response to logon when used as a logon acknowledgement from acceptor back to the logon initiator. | |
| 354 | EncodedTextLen | N | Must be set if EncodedText field is specified and must immediately precede it. | |
| 355 | EncodedText | N | Encoded (non-ASCII characters) representation of the Text field in the encoded format specified via the MessageEncoding field. | |
| Component Block - <StandardTrailer> | Y | |||
Sample Messages
The ^ character is used to represent
SOH character.
8=FIXT.1.1^9=116^35=A^49=BuySide^56=SellSide^34=1^52=20190605-11:51:27.848^1128=9^98=0^108=30^141=Y^553=Username^554=Password^1137=9^10=079^